Trends
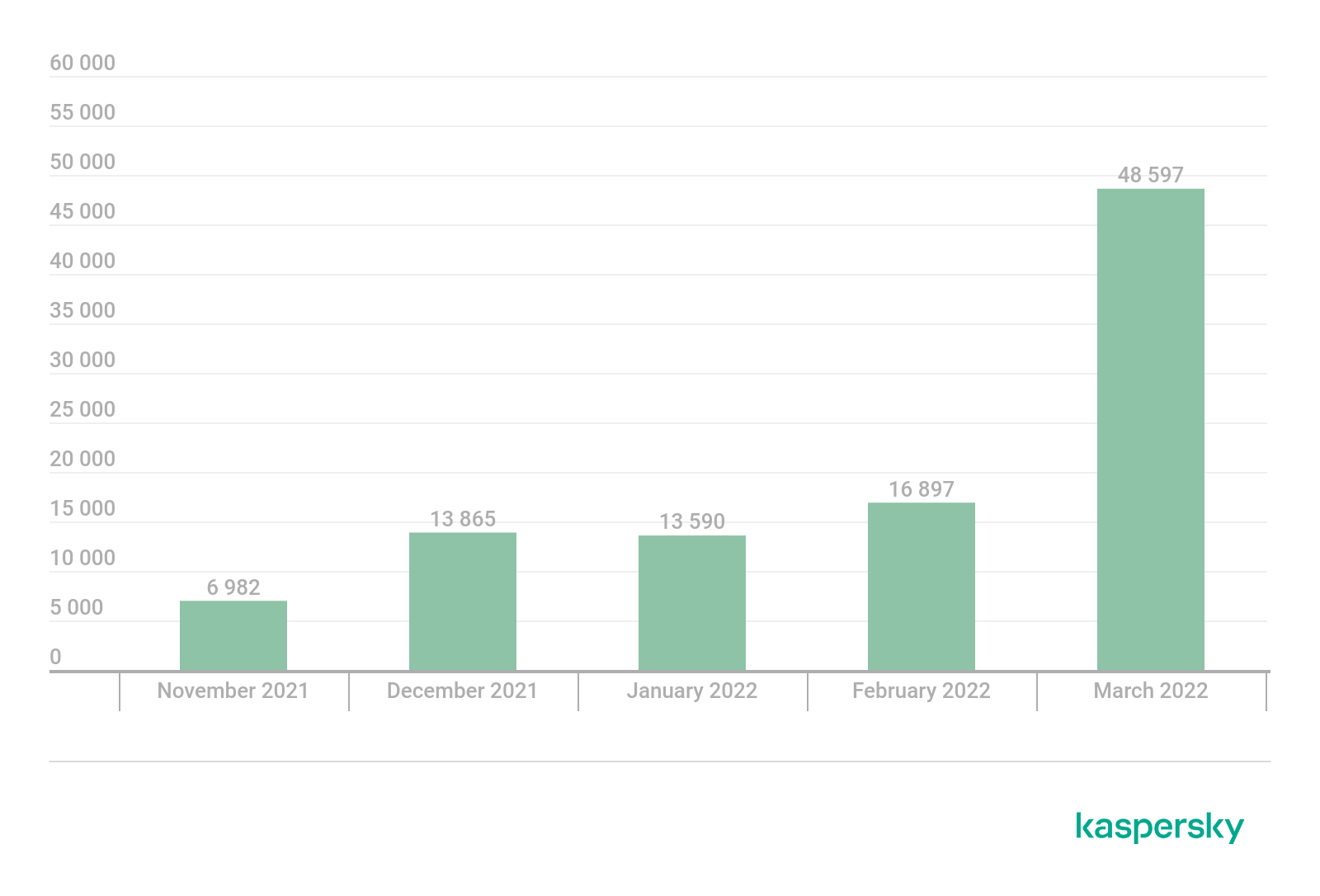
“Most dangerous malware” grew over 200% in March 2022 globally
Emotet is both a botnet, a controlled network of infected devices used for attacks on other devices and malware that is capable of extracting different kinds of data, often pertaining to finance, from infected devices. Operated by experienced threat actors, it has become one of the biggest players in the cybercrime world. Emotet was shut down following a joint effort from various law enforcement agencies from different countries back in January 2021. However, in November 2021, the botnet returned and has been gradually increasing its activity since. Firstly by spreading via Trickbot, a different bot network, and now by itself via the means of malicious spam campaigns.
Kaspersky telemetry shows that the number of victims shot up from 2,843 in February 2022 to 9,086 in March, attacking over three times the number of users. The number of attacks detected by Kaspersky solutions has grown accordingly – from 16,897 in February 2022 to 48,597 in March.
A typical Emotet infection begins with spam e-mails that contain Microsoft Office attachments with a malicious macro. Using this macro, the actor can start a malicious PowerShell command to drop and start a module loader, which can then communicate with a command and control sever to download and start modules. These modules can perform a variety of different tasks on the infected device. Kaspersky researchers were able to retrieve and analyze 10 out of 16 modules, with most having been used by Emotet in the past in one form or another.
The current version of Emotet can create automated spam campaigns that are further spread down the network from the infected devices, extracting emails and email addresses from Thunderbird and Outlook applications and collecting passwords from popular web browsers, such as Internet Explorer, Mozilla Firefox, Google Chrome, Safari and Opera, to gather the account details of various email clients.
“Emotet was a highly advanced network that haunted many organizations around the world. Its takedown was a significant step towards decreasing threats worldwide by helping to tear apart their network and removing it from the top threat list for over a year. While the number of attacks is not comparable to the previous scale of Emotet’s operations, the change in dynamics points to a significant activation of the botnet’s operators and a high likelihood of this threat spreading further in the coming months,’ comments Alexey Shulmin, security researcher at Kaspersky.
CT Bureau











You must be logged in to post a comment Login