Company News
Whatsapp Web announces additional security layer for encryption
Since WhatsApp introduced multi-device capability last year, we’ve seen an increase in people accessing WhatsApp directly through their web browser via WhatsApp Web. With this shift in mind, we’ve been looking at ways to add additional layers of security to the WhatsApp Web experience. Starting today, you can now use Code Verify, an open source web browser extension that automatically verifies the authenticity of the WhatsApp Web code being served to your browser. Code Verify confirms that your WhatsApp Web code hasn’t been tampered with or altered, and that the WhatsApp Web experience you’re getting is the same as everyone else’s.
For years, WhatsApp has protected the personal messages you send on WhatsApp Web with end-to-end encryption as they transit from sender to recipient. But security conscious users need to be confident that when WhatsApp Web receives these encrypted messages, it is protected as well. In contrast to a downloadable mobile app, a web app is usually served directly to users, without a third party reviewing and auditing the code. There are many factors that could weaken the security of a web browser that don’t exist in the mobile app space, such as browser extensions. Additionally, because the mobile app space was built after the web was created, the security guarantees offered on mobile can be stronger, particularly given that third-party app stores review and approve each app and software update. But today, that’s changing, as Code Verify is bringing even more security to WhatsApp Web.
Code Verify works in partnership with Cloudflare, a web infrastructure and security company, to provide independent, third-party, transparent verification of the code you’re being served on WhatsApp Web. We hope this gives at-risk users peace of mind.
No other end-to-end encrypted messaging service has this level of security for people’s communications on the web. In addition to deploying Code Verify for WhatsApp Web, it is also being offered as open source so that other services can use it as well. Below is an overview of how Code Verify works, how to use it, and the value of open-sourcing it.
How Code Verify works
Code Verify expands on the concept of subresource integrity, a security feature that lets web browsers verify that the resources they fetch haven’t been manipulated. Subresource integrity applies only to single files, but Code Verify checks the resources on the entire webpage. To do this at scale, and to enhance trust in the process, Code Verify partners with Cloudflare to act as a trusted third party.
We’ve given Cloudflare a cryptographic hash source of truth for WhatsApp Web’s JavaScript code. When someone uses Code Verify, the extension automatically compares the code that runs on WhatsApp Web against the version of the code verified by WhatsApp and published on Cloudflare. If there are any inconsistencies, Code Verify will notify the user.
While comparing hashes to detect files that have been tampered with is not new, Code Verify does so automatically, with the help of Cloudflare’s third-party verification, and at this scale for the first time. WhatsApp’s security protections, the Code Verify extension, and Cloudflare all work together to provide real-time code verification. Whenever the code for WhatsApp Web is updated, the cryptographic hash source of truth and extension will update automatically as well.

Cloudflare has provided a deeper dive on how this system works, including their role as a trusted third party, on their blog which can be found here.
How to use Code Verify
The Code Verify extension is offered by Meta Open Source and will be available on the official browser extension stores for Google Chrome, Microsoft Edge, and Mozilla Firefox. The extension doesn’t log any data, metadata, or user data, and it does not share any information with WhatsApp. It also does not read or access the messages you send or receive. In fact, neither WhatsApp nor Meta will know whether someone has downloaded the Code Verify extension. Additionally, the Code Verify extension never sends messages or chats between WhatsApp users to Cloudflare.
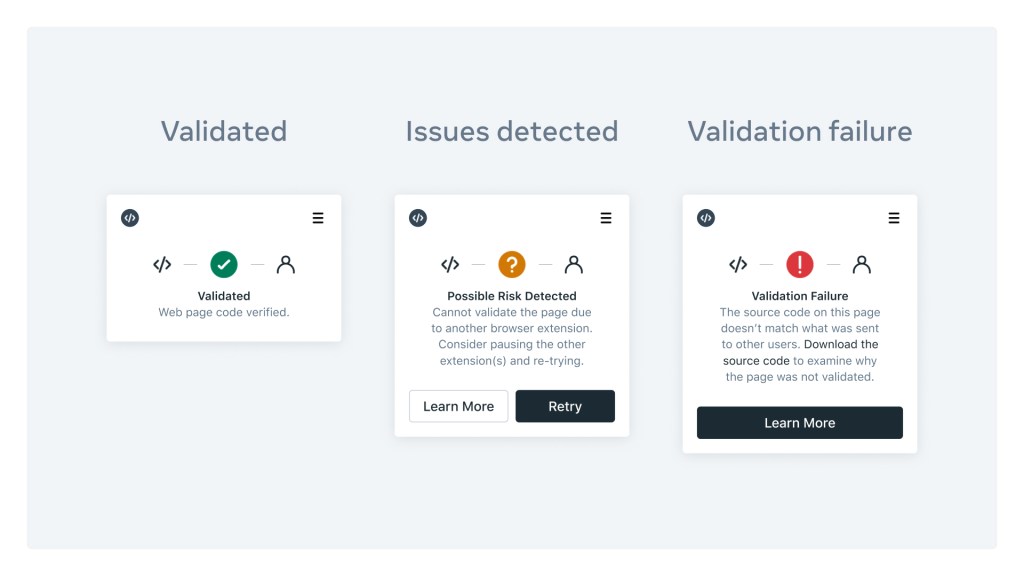
Once installed, Code Verify will run automatically when you go to WhatsApp Web and act as a real-time alert system for the code you’re being served on WhatsApp Web. Pinning the extension to your web browser’s toolbar will allow you to see its findings without any additional steps. You can think of Code Verify as a traffic light for your WhatsApp Web code:
- Code Verify will run immediately, and if the WhatsApp Web code is fully validated, the Code Verify icon in the browser will appear green (see below).
- If the Code Verify icon appears orange (see below), it means that you need to refresh your page or another browser extension is interfering with Code Verify. In this instance, Code Verify will recommend that you pause your other browser extensions.
- If the Code Verify icon appears red (see below), it will indicate that there is a possible security issue with the WhatsApp Web code you’re being served.
Open source for others to leverage as well
Code Verify is available on GitHub. Open-sourcing the Code Verify extension has a few important benefits. First, it allows other companies, groups, and individuals to apply this same level of transparency to their own applications and freely share new ideas with one another to help improve the feature. Second, it puts the power of transparency squarely in the hands of the people. As a browser extension that exists independently of WhatsApp and its infrastructure, people can see for themselves that the extension hasn’t been tampered with. Third, that same discoverability also protects the extension itself. Since it exists in the public eye, it can benefit from the protections of a watchful open source community.
We believe that with Code Verify, we are charting new territory with automatic third-party code verification, particularly at this scale. We hope that more services use the open source version of Code Verify and make third-party verified web code the new norm. And in doing so, we hope this helps bring additional security protections to people all over the world and move the entire industry forward.
CT Bureau














You must be logged in to post a comment Login