CT Stories
The enterprise networking industry

As the COVID pandemic uncertainty refuses to fade, tech dependency is increasing. Enterprises that are in their second phase of digital transformation and have automated more parts of their networks are finding the going relatively easy.
Enterprises worldwide are feeling the strain caused by the COVID-19 pandemic as users work from home, hold virtual meetings, attend online classes as students, and stream online. Network traffic is increasing, resulting in slowdowns and congestion, a reality that has been confirmed by crowd-sourced network data. Telecom companies are ensuring that infrastructure is in place to handle the surge, while acknowledging that connection and accessibility issues have taken place.
Remote work means executives are working more autonomously than ever before. Organizations have to be clear about their goals and each one’s roles. Each needs to know what is expected and also be willing to take on new responsibilities as the situation demands it. And everyone has to constantly share clear, actionable information.
Security and reliability of residential internet-access services and home-networking environments is of major concern. So far, ISPs have not seen a rise in performance problems, although chokepoints at cloud service providers may emerge soon.
One aspect, which is being completely overlooked is network privacy. It appears, in a rush to keep the executives safe and working at home, many companies failed to consider such risks. The easiest way to protect from this is establishing a VPN for employees working from home and encrypting all of the data. It will create a little bit more strain on the company’s IT networks and departments. It may also slow down the connections because it will add additional overheads, and the encrypting and decrypting data may increase latency and jitter. This is, of course, already compounding on the problem of having limited capacity in the home. Many connections are also asymmetrical and have faster download speeds than upload speeds, creating a huge amount of problem, particularly when video conferencing and uploading large digital files. In some cases, VPN gateways may simply not be able to accommodate so many users connecting at once.
Companies are relying more heavily on videoconferencing. Videoconferencing apps are providing a convenient alternative to face-to-face meetings during the outbreak. Videoconferencing providers have responded to the increased need for their services by extending the capabilities of their free offerings. Cisco is now allowing meetings of unlimited length for up to 100 participants on the free version of Webex. Microsoft is giving out six-month licenses to Office 365 that provide access to a more robust version of Microsoft Teams than is usually available for free. Zoom has lifted the 40-minute cap on free meetings in China. The vendors hope the uptick in usage will continue even after fears about the virus subside. Free offerings can be an effective way to generate paying customers.
Data-center operators, although trained to anticipate upheaval due to fires, floods, power outages and other catastrophic events, are finding themselves in uncharted territory.
As a result of the pandemic, tech dependency is increasing. The number of teleworkers is skyrocketing, online retail is surging, business-to-business communications are taking place digitally, and social interactions are moving online.
The year that was
Businesses are entering the second phase of digital transformation by automating more parts of their networks. Most companies have mastered automation of individual tasks by digitizing IT and business processes. They are now in their second phase, where the focus is shifting to reducing complexity and supporting apps with a consistent set of services. These include external-facing apps that generate revenue, and the internal-facing ones, like productivity and operational apps, vital to digitizing business processes.
Network automation has been a game changer. The scale and complexity of networks is greater than it ever was before, and yet for many it is still in its infancy. The enterprises have automated firewall configurations, or the monitoring of their switches and traffic. They might even have looked for security issues. But they are still wading, rather than diving.
In the last five years, the concept of virtualization and software-defined networking has shaped the technology ecosystem of enterprise IT infrastructure. This rapid change is driven because of the usage of cloud services along with an explosion in the Internet of Things (IoT) paradigm. Network admins are focusing on managing and defining policies to all the connected devices from one pane of glass in an automated and intelligent way.
SD-WAN. Software-driven Wide Area Networks (SD-WANs) create more flexible infrastructures that can adapt to changing traffic requirements, which become necessary as more enterprises move to hybrid clouds. They primarily are becoming popular as traditional enterprise WANs are increasingly not meeting the needs of digital businesses, especially as it relates to supporting SaaS apps and multi- and hybrid-cloud usage. Enterprises are interested in easier management of multiple-connection types across their WAN to improve application performance and end-user experience – hence the growth of SD-WAN technologies.
SD-WAN is replacing routing and adding application-aware path selection among multiple links, centralized orchestration and native security, as well as other functions. Consequently, it includes incumbent and emerging vendors from multiple markets (namely, routing, security, WAN optimization, and SD-WAN), each bringing its own differentiators and limitations, says a Gartner report.
One of the biggest changes for 2020 could come around the SD-WAN. One of the drivers stems from the relationships that networking vendors such as Cisco, VMware, Juniper, Arista, and others have with the likes of Amazon Web Services, Microsoft Azure, Google Anthos, and IBM RedHat.
SD-WAN is critical for businesses adopting cloud services, acting as a connective tissue between the campus, branch, IoT, data center, and cloud. It brings all the network domains together and delivers the outcomes business requires. With the WAN in transition, incumbents make their move through acquisitions, while startups continue to innovate at the edge.
“SD-WAN continues to be one of the fastest-growing segments of the network infrastructure market, driven by a variety of factors. First, traditional enterprise WANs are increasingly not meeting the needs of today’s modern digital businesses, especially as it relates to supporting SaaS apps and multi- and hybrid-cloud usage. Second, enterprises are interested in easier management of multiple-connection types across their WAN to improve application performance and end-user experience,” opines Rohit Mehra, vice president of network infrastructure for IDC.
Networking incumbents are investing in the SD-WAN market primarily through acquisitions. Several startups have already been taken off the table, snatched up by incumbents seeking to modernize their networking portfolios, that are able to leverage their installed bases in routing and WAN optimization to vault to the head of the market with their SD-WAN acquisitions.
The SD-WAN market is a gold-rush opportunity. IDC expects the SD-WAN infrastructure market to hit USD 5.25 billion in 2023, the leading vendors being Cisco (Viptela), VMware (VeloCloud), Silver Peak, Nokia (Nuage/Alcatel-Lucent acquisition), and Aryaka.
Gartner assesses the leaders slightly differently. According to its latest WAN Edge Infrastructure Magic Quadrant VMware, Cisco, and Silver Peak are the only leaders, while Fortinet, Citrix, Aryaka, and Riverbed are stacked closely as the nearest challengers. Gartner also lists Huawei in the challengers’ quadrant.
Whatever the case, Cisco has managed to stitch together the No. 1 position in the market. IDC’s research finds that Cisco has claimed 46.4 percent of the market, well ahead of No. 2 VMware/VeloCloud, which captured 8.8 percent of the market.
The SD-WAN notable startups include Big Leaf, Cato Networks, CloudGenix, Teridion, Turnium, Versa Networks, and Zenlayer.
As enterprises begin to migrate away from legacy architectures to cloud services and SDN, SD-WAN vendors have begun to layer on new features, such as security services and intelligent, policy-based routing, while also capitalizing on vendor switching headaches by rolling out hybrid and patchwork SD-WANs that help ease the transition from a hardware-dependent reality to a new SDx one.
VPNs. In the last decade, many enterprises, having facilities spread across multiple continents, have adopted digital systems. WANs are extensively used to interconnect those digital systems. However, WANs are mainly built upon telephone leased lines that are too expensive for enterprises. Virtual Private Networks (VPNs) using the internet have emerged as a cost-efficient solution for enterprises. With its tunneling capability, VPN establishes a point-to-point connection between branches/users and servers on the internet, thus tackling the increasing cyber or denial-of-services (DDOS) attacks. It also enables data encryption, and allows device-scanning capabilities for any malware presence on devices. The earlier bottleneck of the network and slow-down in speed reduction in data-related operations has been resolved by the emergence of layer-2 tunneling protocols (L2TP) and virtual private LAN service (VPLS). It is now possible to run latency-sensitive business applications on VPN. Another key benefit is that a VPN establishes a common logical network over the internet that can be accessed from any country.
Another trend that developed a few years back was that tech giants like Google, Facebook, and McAfee launched cloud-based VPN services to replace traditional VPN. This move was a response to be aligned with cloud services offered over the Internet. In upcoming years, cloud VPN will be adopted more as the move to cloud increases.
SASE. The mixture of cloud and security services at the edge will lead to another trend in 2020, one that Gartner terms as secure access service edge (SASE), which is basically the melding of network and security-as-a-service capabilities into a cloud-delivered package. By 2024, at least 40 percent of enterprises will have explicit strategies to adopt SASE, up from less than 1 percent at year-end 2018.
“SASE is in the early stages of development. Its evolution and demand are being driven by the needs of digital-business transformation due to the adoption of SaaS and other cloud-based services, accessed by increasingly distributed and mobile workforces, and to the adoption of edge computing,” maintains Gartner. Early manifestations of SASE are in the form of SD-WAN vendors adding network-security capabilities, and cloud-based security vendors offering secure web gateways, zero-trust network access, and cloud-access security broker services. Regardless of what it is called, it is clear the melding of cloud applications, security, and new-edge WAN services will be increasing in 2020.
Security needs to be automated too. Putting machines in control of things like provisioning, data access, backup, and a host of other functions merely adds more risk to an already risky environment that is now pushing way past the firewall to the cloud and the edge.
While an automated enterprise does pose new security challenges, the fact is that the same tools being used to augment the development and operations side of the house can also be applied to security. And the results are largely the same – faster, more thorough performance, and the ability for security professionals to shed the dull drudgery of their jobs to focus on more important matters. And many security functions are ripe for automation, including change planning, risk assessment, and compliance testing.
Already security teams are falling behind the curve when it comes to protecting critical systems and data. More than three-quarters of security pros do not check out all of the critical alerts that come their way. This is where tools like machine learning (ML) can make a substantial difference. By weeding out the true problems from all the false alarms or routine interrupts, ML can take on much of the security burden while providing a more accurate and timely assessment of current conditions.
Perhaps the most important reason security needs to jump on the automation bandwagon is because hackers and other wrongdoers are most certainly heading in this direction as well. With intelligent automation platforms and codes readily available on the internet, along with the hyperscale cloud resources to use them, the bad guys have all the tools they need to make life miserable for organizations that fail to effectively automate their security postures. Like all other elements in the IT stack, security has to keep up with the times.
Data loss-prevention technology is becoming a critically important security tool in an age of strong data privacy laws. Every organization has data, and some of that data is more sensitive than others. DLP technology provides a mechanism to help protect against sensitive data loss – and thus could also be something of a mitigating factor when dealing with compliance agencies in the wake of a data breach. As such, DLP has become a top IT spending priority.
DLP products and services support the cloud, privacy compliance, data labelling, and machine learning. The leading vendors in this segment include Checkpoint, Code42, Digital Guardian, Fidelis, Forcepoint, McAfee, Proofpoint, and Trend Micro.
Cloud computing. The cloud computing market is expected to grow in multiple folds due to, increase in the adoption of hybrid cloud computing services among major industries to tackle their complex digital transformations and security-related concerns across the regions. For instance, the healthcare organizations are migrating its critical clinical and IT applications such as EHS and PACS on the hybrid cloud to migrate the applications & associated data with the required technical upgradation. Healthcare organizations especially need flexibility, ease of management and security of data that the hybrid cloud fulfills the requirement.
Cloud computing can be attributed in three major deployment models, private, public, and hybrid. Many governments around the world are adopting or increasing their participation in cloud computing technology to bring down their CapEx that they used to spend on their IT infrastructure.
Cloud computing has become ubiquitous because of its agility and cost savings – but along with those benefits have come security concerns. Among the areas addressed by cloud security products are access control, workload security, privacy and compliance, and more. The different categories of solutions include cloud access security brokers (CASB), software-defined compute (SDC) security, cloud workload-protection platforms, and SaaS security.
Leading global cloud-security companies are CloudPassage, FireEye, LaceWork, McAfee, Palo Alto Networks, Qualys, Symantec, Tenable, Trend Micro, and VMware.
 Data centers. Merger and acquisition activity surrounding data-center facilities is huge and private equity firms are taking most of the action. New data from Synergy Research Group shows that in 2019 the number of data center-oriented M&A deals closed passed the 100 mark for the first time. This was up 6 percent from 2018 and more than double the numbers of deals closed in 2016. Over the last five years almost 350 deals have closed. One radical change in 2019 was the dramatic 50-percent increase in private equity deals, which more than offset a sharp 45-percent drop in M&A deals closed by public companies. While deal volume increased in 2019, the aggregate value of those deals declined due to a 24-percent reduction in average deal value, continuing a trend seen in 2018. 2017 marked a peak in average deal values, thanks to three multi-billion-dollar deals and three more valued at over a billion dollars each. The number of billion-dollar deals declined in 2018 and again in 2019.
Data centers. Merger and acquisition activity surrounding data-center facilities is huge and private equity firms are taking most of the action. New data from Synergy Research Group shows that in 2019 the number of data center-oriented M&A deals closed passed the 100 mark for the first time. This was up 6 percent from 2018 and more than double the numbers of deals closed in 2016. Over the last five years almost 350 deals have closed. One radical change in 2019 was the dramatic 50-percent increase in private equity deals, which more than offset a sharp 45-percent drop in M&A deals closed by public companies. While deal volume increased in 2019, the aggregate value of those deals declined due to a 24-percent reduction in average deal value, continuing a trend seen in 2018. 2017 marked a peak in average deal values, thanks to three multi-billion-dollar deals and three more valued at over a billion dollars each. The number of billion-dollar deals declined in 2018 and again in 2019.
Since the beginning of 2015, Synergy has identified 348 closed deals with an aggregated value of USD 75 billion. Over the five-year period, the aggregated deal value has been split roughly equally between public companies and private equity buyers, while private equity buyers have accounted for 57 percent of the deal volume. Since 2015, the largest deals to be closed are the acquisition of DuPont Fabros by Digital Realty, the Equinix acquisition of Verizon’s data centers, and the Equinix acquisition of Telecity. Over the 2015–2019 period, by far the largest investors have been Digital Realty and Equinix, the world’s two leading colocation providers. In aggregate, they account for 31 percent of total deal value over the period. Digital Realty also has a pending deal to acquire Interxion, in what would be the largest-ever data-center transaction. Other notable data-center operators who have been serial acquirers include CyrusOne, Iron Mountain, Digital Bridge/DataBank, NTT, GI Partners, Carter Validus, GDS, QTS, and Keppel.
“The aggressive growth of cloud services and outsourcing trends more generally are fueling a drive for scale and geographic reach among data-center operators, which in turn is stimulating data-center M&A activities. This has been attracting an ever-increasing level of private equity activity as investors seek to benefit from high-value and strategically important data-center assets. It is also notable that even the biggest publicly traded data-center operators are increasingly turning to joint ventures with external investors to help fund growth and protect balance sheets,” says John Dinsdale, a chief analyst at Synergy Research Group.
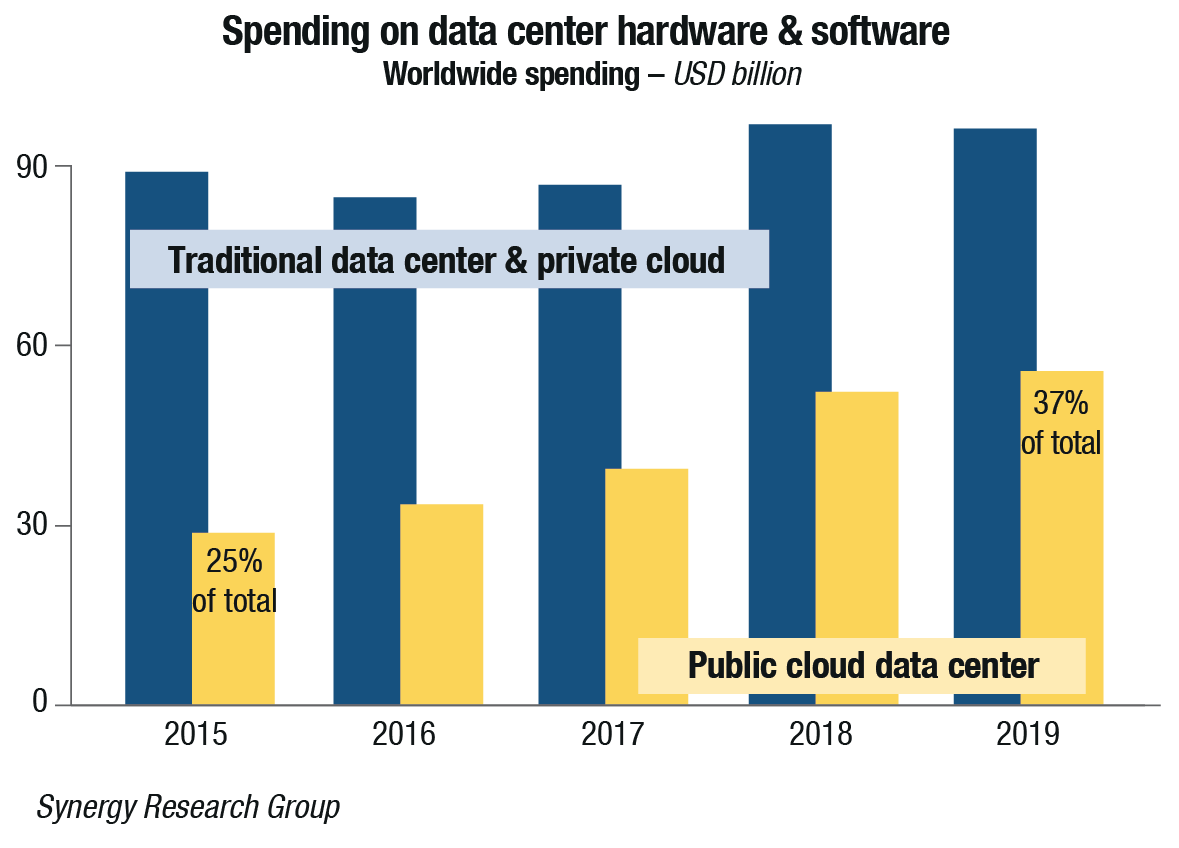
The total data-center infrastructure spending data covers both cloud and non-cloud service provider and enterprise data center, hardware, and software. By product, the data covers servers, OS, storage, networking, virtualization software, network security, and management software. Servers are the largest product category, and it accounted for 46 percent of hardware and software spending in 2019. Vendor market-share ranking in 4Q 2019 showed the leaders being Dell, Microsoft, HPE, and Cisco. They were followed by Huawei, IBM, VMware, Inspur, and Lenovo. In the public cloud segment, ODMs once again accounted for the biggest share of the market. They also benefited from a big year-end spike in shipments to hyperscale operators, thereby enjoying a record quarter.
“Cloud service revenues grew by 39 percent in 2019, enterprise SaaS revenues grew by 26 percent, search/social networking revenues grew by 20 percent, and e-commerce revenues grew by 24 percent, all of which helped to drive increases in spending on public-cloud infrastructure,” asserts Dinsdale. “Meanwhile, enterprise spending on their own data centers is being crimped by the shift in workloads to public clouds. We are already seeing server shipments to public-cloud providers outstripping shipments to enterprises and that trend will continue.”
 Private 5G. 5G promises dramatically faster speeds, lower latency, and increased capacity than today’s 4G LTE technology. It is also a potential alternative to Wi-Fi, with greater reliability and performance in industrial settings.
Private 5G. 5G promises dramatically faster speeds, lower latency, and increased capacity than today’s 4G LTE technology. It is also a potential alternative to Wi-Fi, with greater reliability and performance in industrial settings.
Coverage, standards, and device support still are not where they need to be for full deployment, but that is not stopping some companies. Early adopters are rolling out 5G initiatives while standards, devices, coverage evolve.
Gartner places 5G at the peak of inflated expectations in its most-recent hype cycle report and predicts that it will take two to five years before 5G reaches what the analyst firm calls the plateau of productivity, when mainstream adoption starts to take off.
Until that happens, many enterprises are circumventing the lack of coverage by deploying private 5G in factories, college campuses, hospitals, office buildings, or other contained environments. But setting up 5G is not as easy as buying a Wi-Fi router and plugging it into the network. For starters, the 5G spectrum is controlled. As a result, companies have three main options. They can get spectrum from the public providers; they can buy their own spectrum; or they can use the general authorized-access public spectrum that has been approved for commercial 4G and 5G use in their respective countries. Meanwhile, devices makers have been working to release gear that can take advantage of 5G networks.
But it is not enough to have 5G radios and antennae. IoT devices like robot arms, security cameras, and automated vehicles, may need to be reengineered to take advantage of 5G capabilities. Multiple parts have to work together, and they are not all in place yet. The initial deployments of 5G are actually a hybrid of 4G and 5G. The data is 5G, but the controls for the network are 4G because all the network control infrastructure today is 4G.
Likewise, early adopters will have to wait for 5G standards to develop further before promised attributes – including higher bandwidth, lower latency, and support for more devices – become a reality!














You must be logged in to post a comment Login