Trends
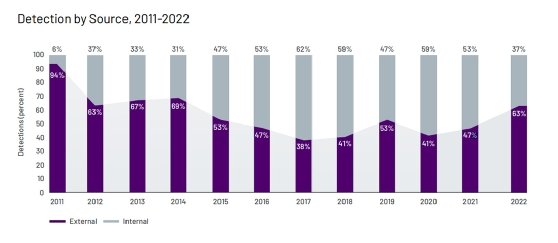
63% of breaches were discovered externally in 2022
Organizations were notified that a breach had occurred from an external party in 63% of the cases Mandiant tracked last year, according to a new report from the Google Cloud subsidiary.
Threat intelligence firm Mandiant, which was acquired by Google last year, published on Tuesday its “M-Trends 2023” report, dedicated to threat intelligence insights the vendor gained in 2022. Key topics in the report include breach notification, threat actor behavior and nation-state activity.
The 63% figure is an increase from 47% in 2021 and the highest share of breach victims being notified externally since 2014. Although an “external party” can include both security partners and adversaries, Mandiant said 2022’s increase is likely affected by Mandiant proactively investigating and responding to cyber threat activity targeting Ukraine.
Ransomware results were even more pronounced — victims were notified by external sources in 70% of incidents. Mandiant said in those cases, organizations were notified via a ransom note 67% of the time and security partners the other 33%.
Nick Richard, Mandiant senior manager at Google Cloud, told TechTarget Editorial that while Mandiant didn’t provide figures in the report for non-ransomware events, “it is generally not very common” for breach victims to be notified by adversaries.
Dwell time — the amount of time a threat actor remains undetected in a victim environment — overall saw major improvements in 2022, Mandiant said. The M-Trends report saw median dwell time drop from 21 days in 2021 to 16 days in 2022. The decline represents improvements in dwell times of threat actors where notifications come internally (18 days in 2021 to 13 days in 2022) and externally (from 28 days to 19 days).
“Notable improvement in global median dwell time where an external entity was the notification source may indicate that organizations respond to external notifications more quickly,” the report read. “This reflects a growing recognition of the critical role partnerships and information exchange play in building a resilient cybersecurity ecosystem.”
Mandiant said that as security partners improve the quality of external notifications, “the improvement of information sharing will enable organizations to act more effectively than if left to identify similar intrusions on their own.”
In cases of ransomware, median dwell time increased overall from five days in 2021 to nine in 2022. Richard said regional findings “certainly” affected the increase. While the Americas stayed consistent year over year, Asia-Pacific ransomware dwell time doubled, and Europe, the Middle East and Africa rose 89%.
“The key message remains that ransomware operators tend to operate very quickly and have short dwell times,” Richard said.
The report noted, however, that ransomware’s share of total investigations Mandiant participated in declined, from 23% in 2021 to 18% last year. Although the number appears to line up with other vendor statistics that suggest an “improvement” or “decline” in ransomware overall, the reality of the situation is more complicated.
In a press release that accompanied the report, Sandra Joyce, vice president of Mandiant Intelligence at Google Cloud, wrote that “multiple shifts in the operating environment” likely contributed to the drop in ransomware attacks Mandiant responded to last year. These shifts included ongoing law enforcement efforts targeting ransomware, Russia’s invasion of Ukraine, and organizations improving their response to and protection from ransomware attacks. TechTarget














You must be logged in to post a comment Login